Advanced Encryption Standard (AES) Origins clear a replacement for DES was needed ◦ have theoretical attacks that can break it. ◦ have demonstrated exhaustive. - ppt download

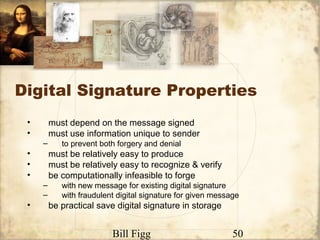
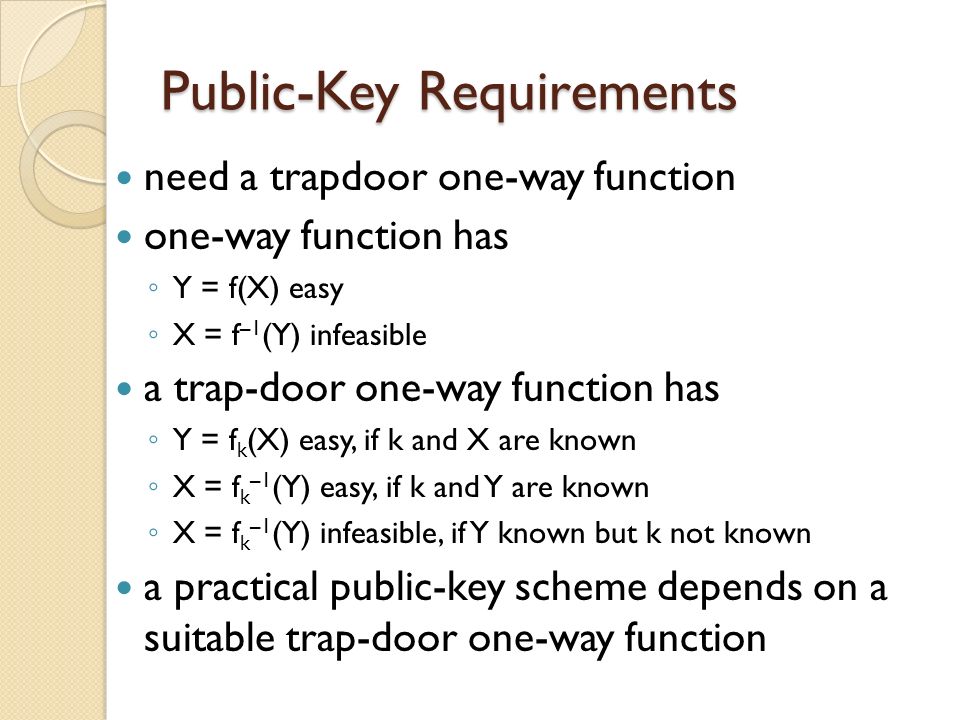
Transitive Signatures based on Factoring and RSA Mihir Bellare (University of California, San Diego, USA) Gregory Neven (Katholieke Universiteit Leuven, - ppt download
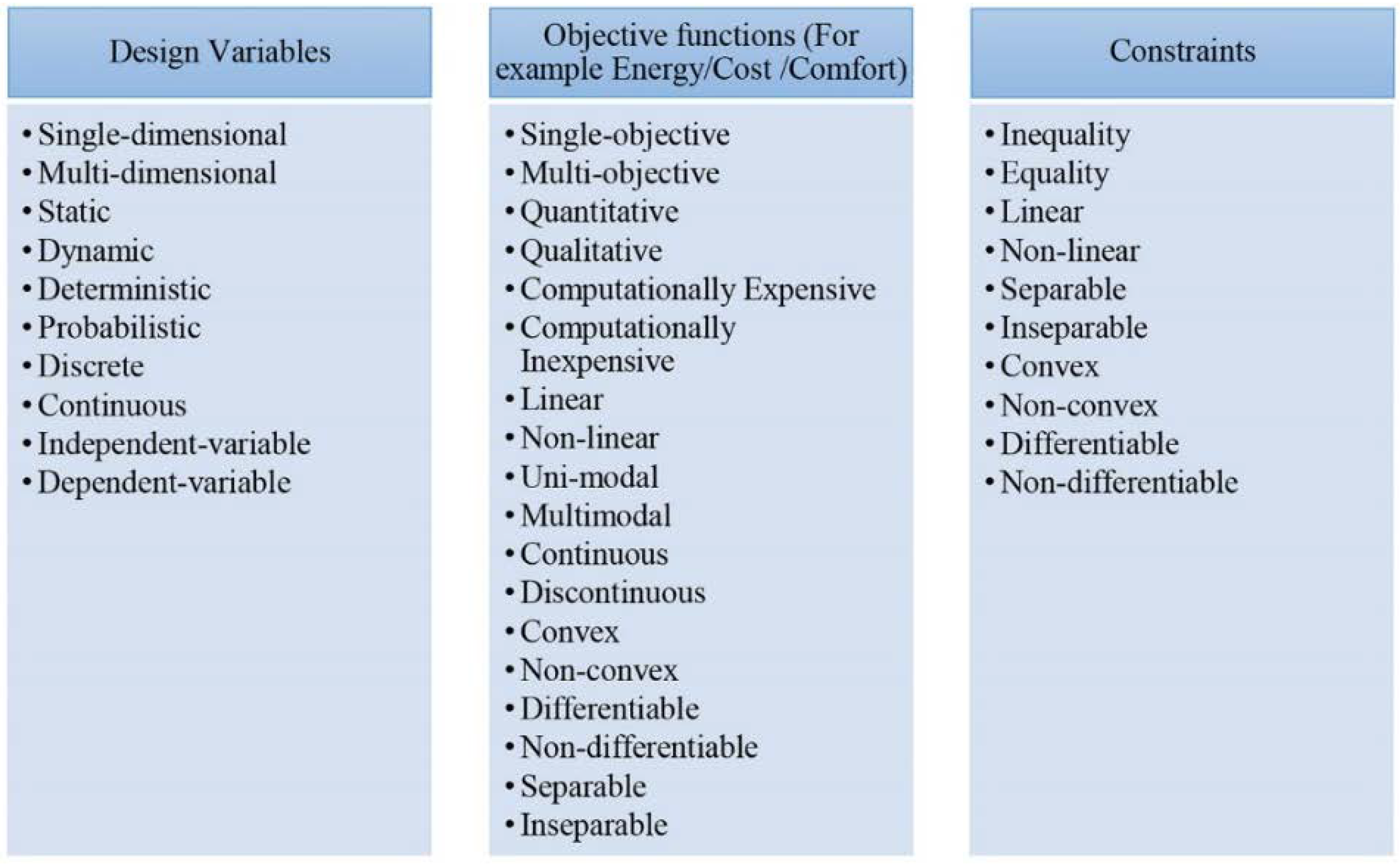
Sustainability | Free Full-Text | Performance Assessment of Algorithms for Building Energy Optimization Problems with Different Properties | HTML
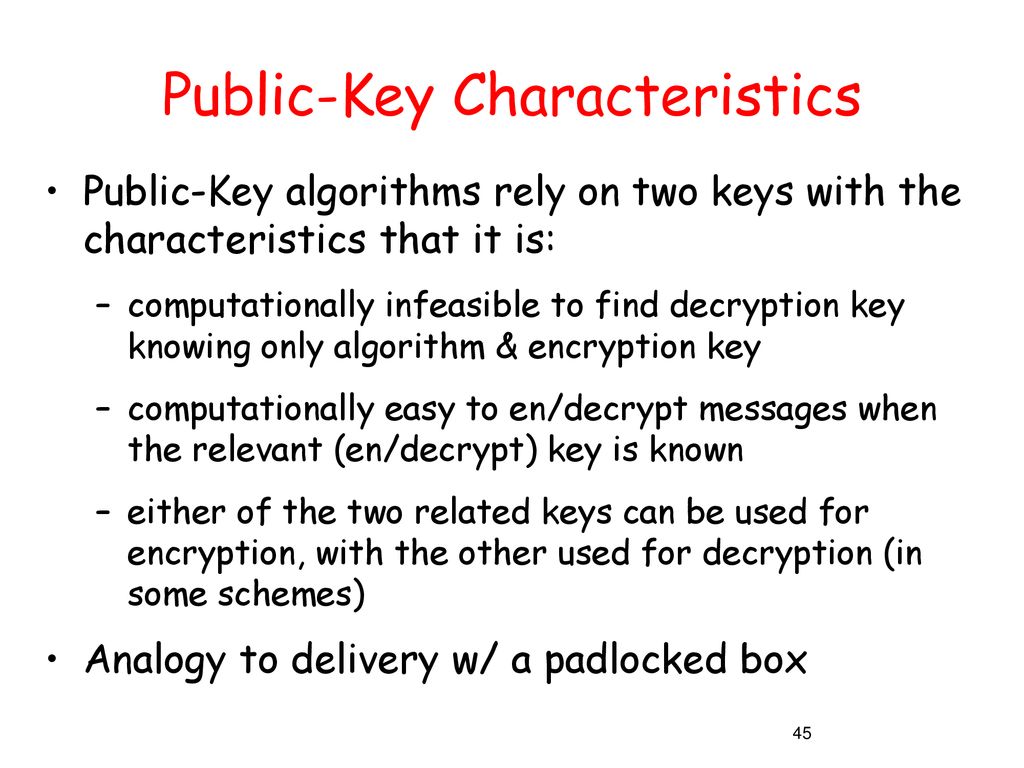
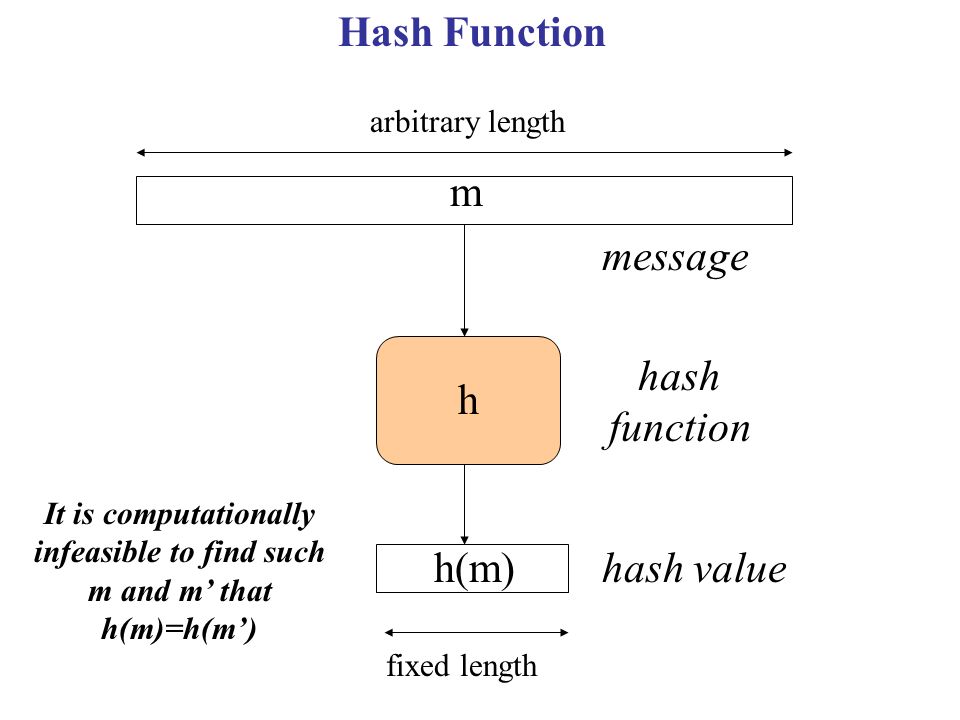
Why Computer Security The past decade has seen an explosion in the concern for the security of information Malicious codes (viruses, worms, etc.) caused. - ppt download
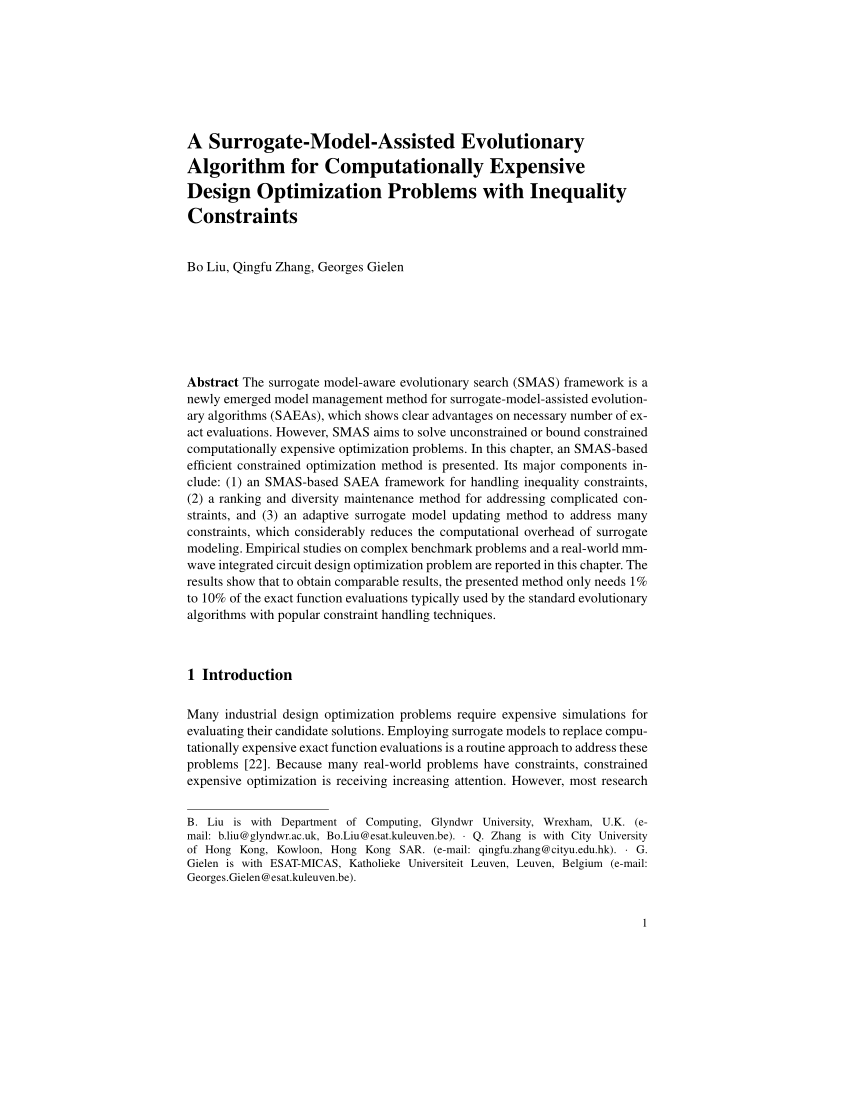
PDF) A surrogate model assisted evolutionary algorithm for computationally expensive design optimization problems with discrete variables